Non‐interactive deniable ring signature without random oracles - Zeng - 2016 - Security and Communication Networks - Wiley Online Library

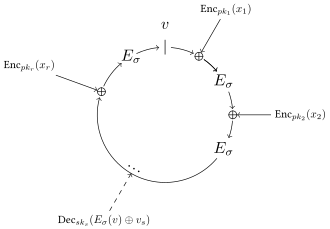
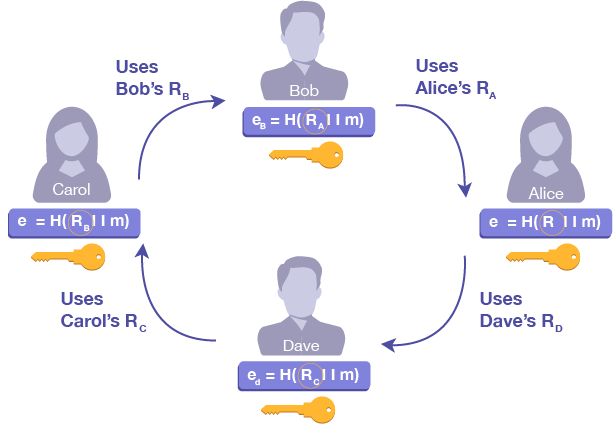
The ring signature paradigm. The equation is verified if z = v. Given... | Download Scientific Diagram

The ring signature paradigm. The equation is verified if z = v. Given... | Download Scientific Diagram

The ring signature paradigm. The equation is verified if z = v. Given... | Download Scientific Diagram
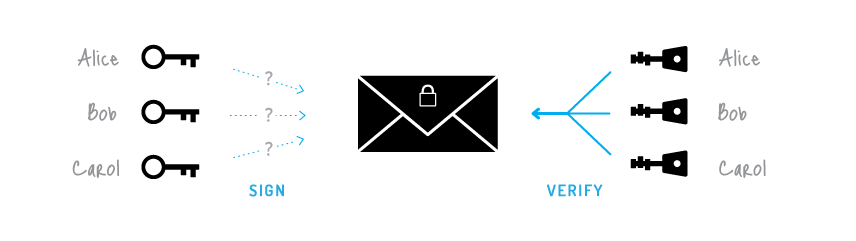
![Go and Link Some Ring Signatures. A demo of the method is [demo]. | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium Go and Link Some Ring Signatures. A demo of the method is [demo]. | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium](https://miro.medium.com/max/1400/0*nkdqhi4uvgluGc2R.png)
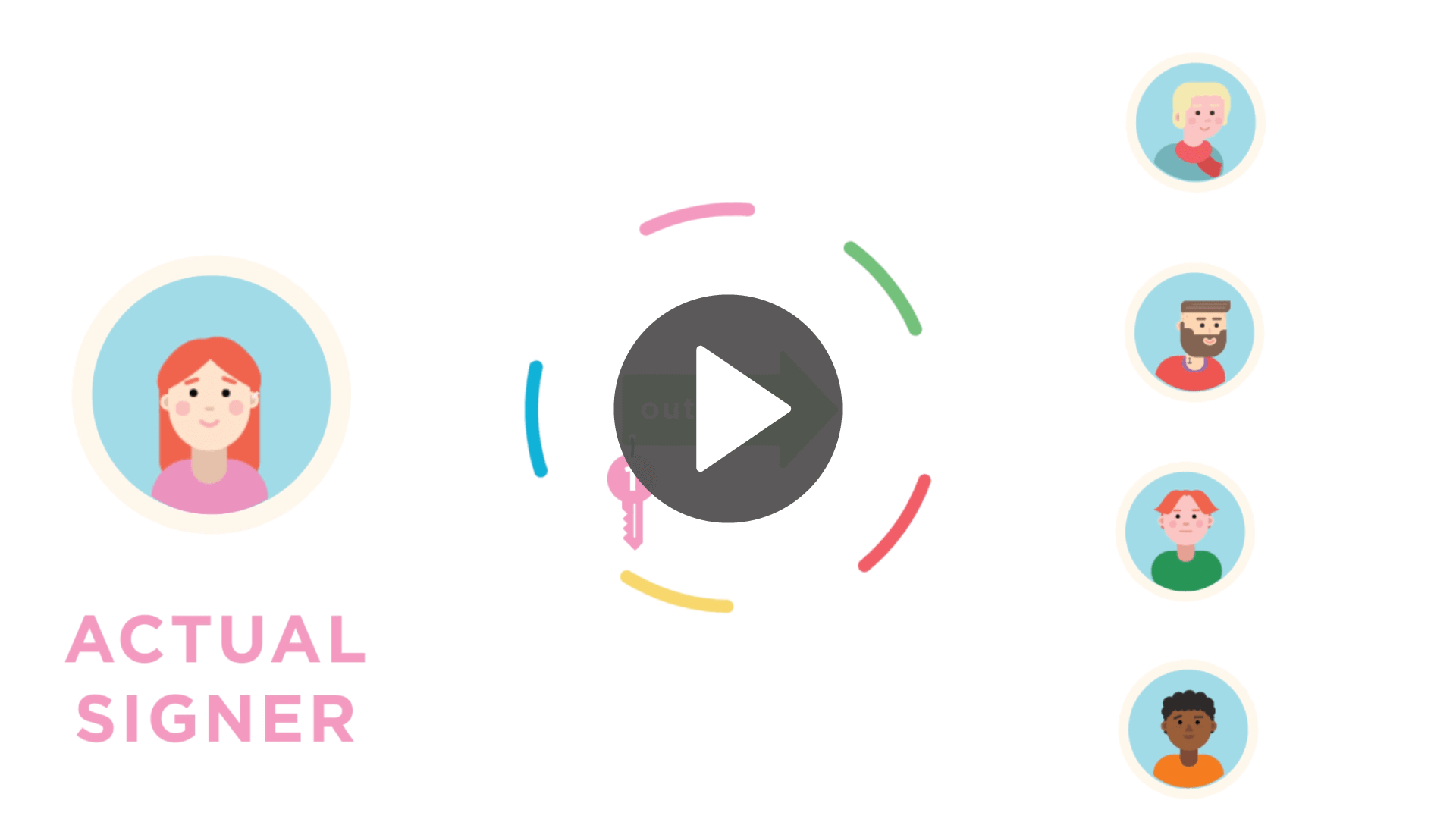
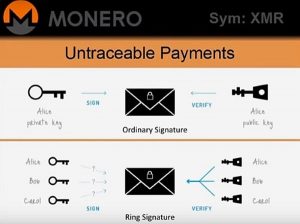
Go and Link Some Ring Signatures. A demo of the method is [demo]. | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium
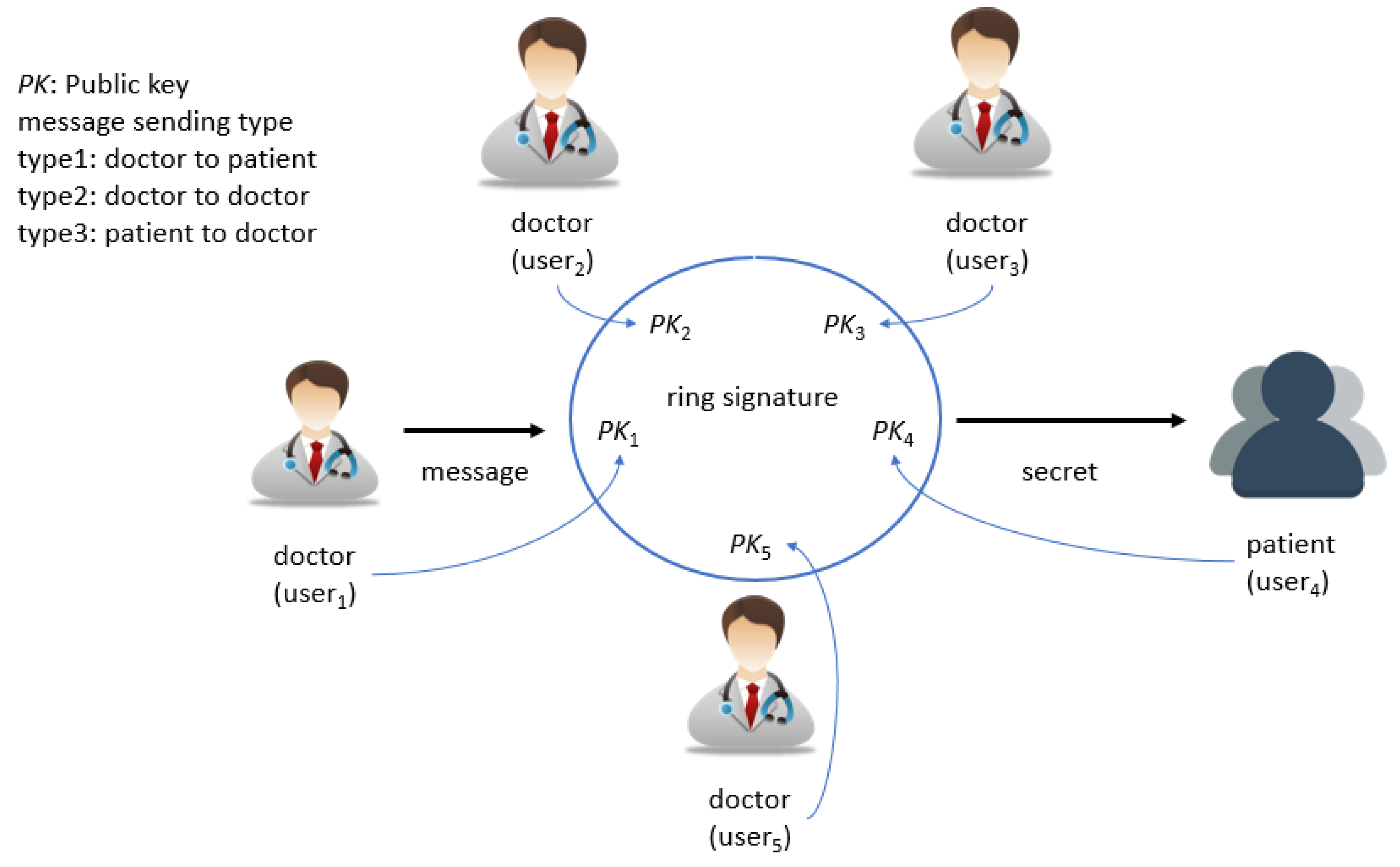
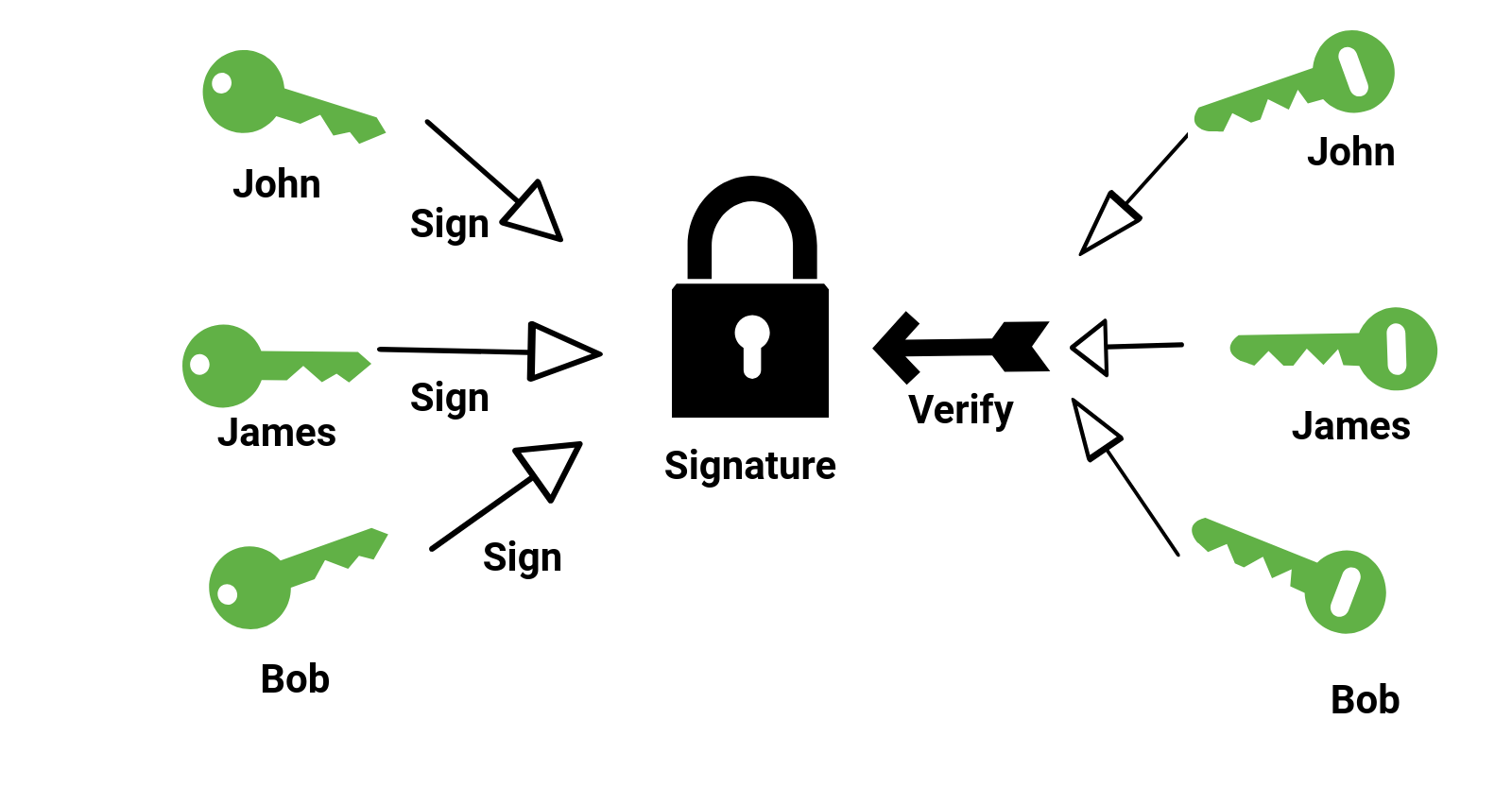
Symmetry | Free Full-Text | A Ring Signature Based Anonymity Authentication Scheme for Group Medical Consultation | HTML
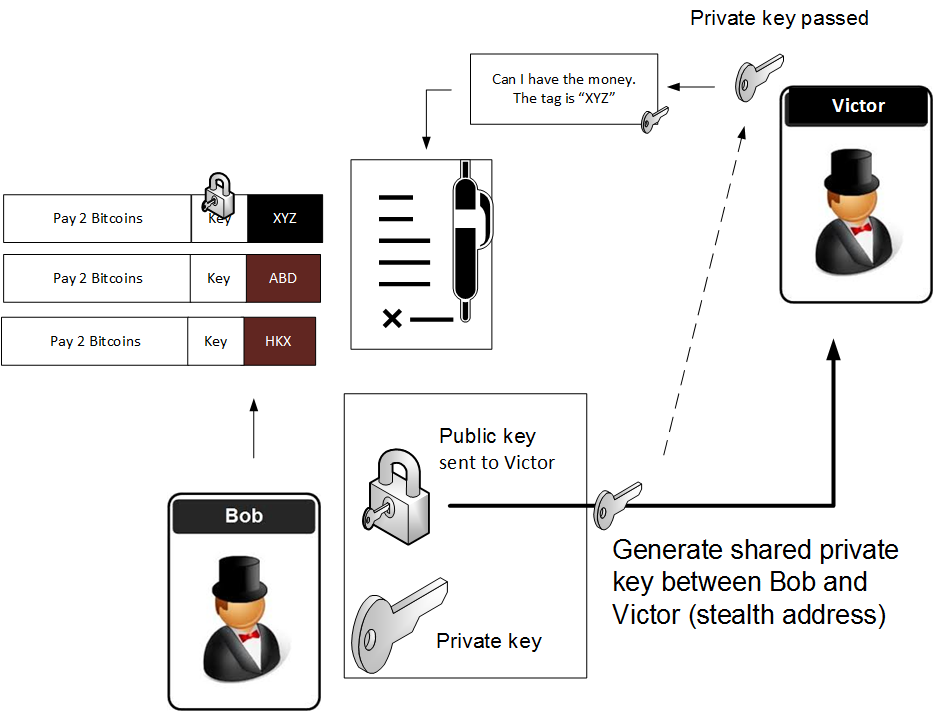
Linkable Ring Signatures, Stealth Addresses and Mixer Contracts | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium